If you're looking to buy or sell items online in Pakistan, free classified websites can…
Trojan horse Malware in cyber-attack | How it harm to Devices?
Learn all important things about Trojan malware…its mythology, effects, types, and how to defend the devices and PC from it.
advertisement
Definition of Trojan
“A Trojan horse or Trojan is a kind of malware that keeps hidden its actual content to make fool a user into thinking that it is a safe file. Trojan horse virus downloads on a computer as an authorized file but is disguised”.
Trojan horse myth
The mythology behind the Trojan horse is well-known. In the odyssey, it is described how Greek soldiers used a wooden horse to sack the city of Troy. When the belly of the horse opened it was too late and the Greeks succeeded in capturing the city. This wooden horse was helped soldiers to enter and win the war after 10 years besieged. Thousands of years later, this myth of the Trojan horse is still alive.
Like this, the Trojan term was introduced in Trojan War. It is now used as the name of “Trojan horse” in computing that applied deceivingly benign computer coding.
What does the Trojan horse do?
advertisement

A Trojan is unknown to the user. Users must know how Trojan works and what the impact of Trojan on devices is. Like a wooden horse was used to sack troy, a computer is also used to carry the payload and it acts as a delivery channel for entrance to a variety of threats. Trojan horses contain benign codes that seem like authorized applications but are written to disrupt or damage computer programming and steal personal information.
Mostly, the virus can replicate itself and auto-execute. A Trojan malware cannot. A user helps to execute this Trojan. Even Trojan viruses and Trojan malware often work vice versa
Here is an example of Trojan malware to explain to you how it works.
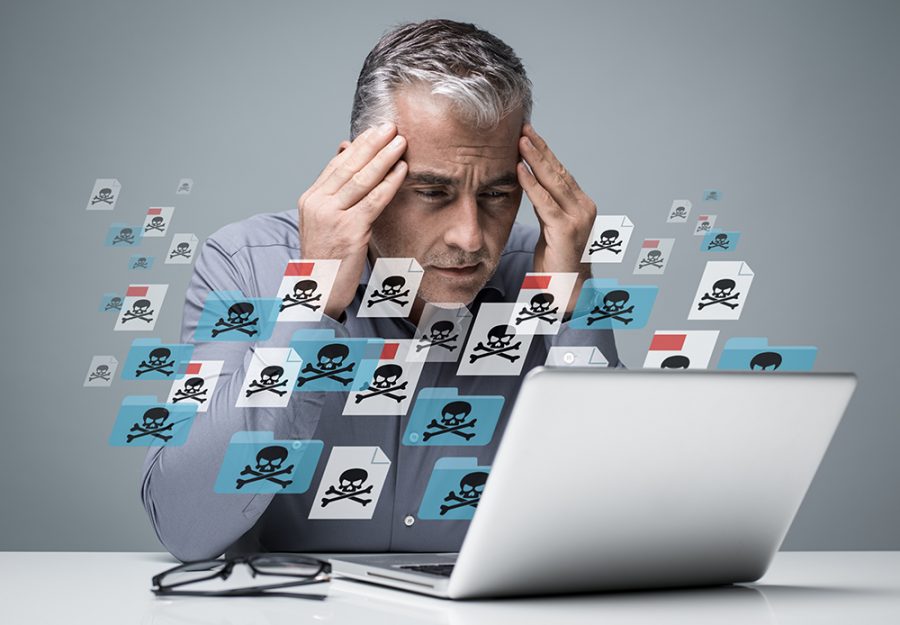
Maybe you are thinking that you have received an email from someone and clicked on it that looks like an authorized attachment. But you have been deceived. The email is from a cyber-attacker. When you click on it, downloaded and opened, it has started to install the malware on your PC or any device.
So, when you run the program, that installed malware spread to all files and harms your computer. The Trojan horse has designed to work for various things.
Effect of Trojan horse on computer
advertisement
Trojan highly affects mobiles and computers. They can damage the information or files on a hard disk. Trojan malware can also resend and capture personal data from an outsider. It can allow an intruder, to open the communication ports and control the infected device remotely. Trojan does this by recording keywords, and strokes, reading passwords or opening the way to additional malware.
Actions of Trojan malware can include:
- Blocking data and files
- Deleting files
- Modifying data
- Copying the sensitive data
- Disturbing the computer performance
- Disrupting networks
Types of Trojan horse attacks
Trojan horse malware has various common types. Here is a look at all Trojan types with names and what they do with your devices.
1. Backdoor Trojan

Backdoor Trojan allows attackers to control a computer through remote access. The Backdoor Trojan horse is one of the most potentially harmful and simplest types of Trojan. Trojan malware itself creates the backdoor on your device.
advertisement
Its purpose is often to download, upload malware, or execute the dangerous file at the user's will and ensure that the device or computer is vulnerable to threat. The activity of the Trojan backdoor is to set up the botnets. Your computer becomes part of zombie botnets without your knowledge. Furthermore, the backdoor allows the code and gives a command to be executed on your computer and then monitor your website traffic.
2. Rootkit
The meaning of rootkit is root (a traditional term for a privileged account on a UNIX-like of operating system) and kit refers to (the component of software that execute the tool). Rootkit virus is designed to hide certain activities or objects in devices. The purpose of a rootkit is to prevent harmful or malicious programs from being detected by anti-rootkit software. The main aim of a rootkit Trojan is to extend the duration of the malicious program so it can execute, and do maximum damage to your device.
3. Exploits Trojan
Exploit is a type of Trojan attack that contain code or data and take advantage of susceptibility within an application. These exploits inject a code containing a device that was deliberately designed. Unlike other malware, exploit is not inherently virus, but still is used for wicked purposes. In exploit activity, code may be used to carry or deliver malware but that code is not malware itself.
4. Banker Trojan
Banker Trojan is also known as Tiny Banker Trojan (TBT), or Tinba. It is specially designed for attacking online banking and targets to steal personal information like transactions, bill pay data, and credit card information. A tiny Trojan banker was first discovered in 2012 when thousands of Turkish computer was initially infected. It is the most widespread Trojan among all other types. The carelessness of users as well as the increasing acceptance of online transactions and banking are giving easiness to cyber criminals. Cyber attackers easily obtain access to personal credentials to bank accounts.
5. DDoS attack Trojan
DDoS is a Disturbed Denial of service Trojan. This is programmed to execute DDoS attacks, where any machine or network is disabled by a flood of applications from various sources. DDoS Trojans continue to haunt the website. In these threats, a network or server is torpedoed with requests by botnets. The traffic that comes from your PC is to take down network traffic.
advertisement
For example, in mid-June 2020, Amazon fended off a record DDoS attack online on the server. For the next three days, the website of amazon was targeted with throughput data of 2.3 terabytes per second. There must be a boundless and powerful botnet to achieve that computing power. These botnets consist of zombie computers and they are working silently as attackers.
6. Downloader / Dropper Trojan
Downloader Trojan is files that are written to download additional viruses and malware onto the device. It targets an already infected device or PC, and downloads and installs the updated version of the malicious computer program. Dropper Trojan can include adware. One of the famous dropper Trojans is Emotent malware that has been exhibiting harmless but in contrast to creating a backdoor, that cannot execute itself on a computer. Downloader trojan brings other various malware with it that’s why it is also called dropper. For example, banking Trojan carries Trickbot and ransomware Ryuk.
7. Game-thief Trojan
This type of Trojan steals user account data and information from online players and gamers. Game thief trojan is a malicious program that is designed to control online gamers' requests, web, FTP, Email, and other ways may also be used to transport the stolen data.
8. Mailfinder Trojan
Mailfinder Trojan haunts the accumulated email addresses from PC or other devices. Additionally, there are other types of this Trojan;
- ArcBomd Trojan
Attacks on windows program
- Notifier Trojan
Notify the signals to cyber-attackers that the infected device is connected to a network
- Clicker Trojan
Appearing to drive traffic to specific sites (fraud) or to drain the budget of a competitor (attack) by artificially inflating the referrals that are paid for.
- Proxy Trojan
Allows cybercriminals to use the target computer as a proxy to connect to the internet
- PSW Trojan
PSW is password stealing ware that launched to search systems in files and steal the confidential registry and data.
advertisement
9. Trojan-Spy
Spy Trojan programs spy on how users use the computer. For example, by tracking data the user enters through a keyboard, getting the list of applications that run on the PC, taking screenshots, etc.
10. Trojan-Ransom
Ransom Trojan modifies the computer data so that the device doesn’t run securely or correctly. Attackers block your data. The cyber-criminal will only run correctly the performance of the computer or unblock data. After that, you have to pay them the money as ransom which they demand.
Some ways to save computers and mobiles against Trojan horse malware
Here are some important dos and don’ts to help protect your devices against Trojan malware.
The Do's
- PC security starts with running and installing a network security suite. Run periodic diagnostic scans with your computer’s software.
- You can set it up so the program runs automatically and scans frequently.
- Update your operating system’s software as soon as updates are made available from the software company.
- Cybercriminals tend to exploit security holes in outdated software programs. In addition to operating system updates, you should also check for updates on other software that you use on your computer.
- Secure your accounts with unique and complex passwords, using numbers, a complex combination of letters, upper case letters, and symbols.
- Keep your credentials secure by applying the firewalls.
- Back up your data on daily basis. If a Trojan harms your devices, this will help you to restore your data.
- Be careful to email attachments. To help stay safe, scan an email attachment first.
The Do not's
- Don’t visit harmful or unsafe websites and pages. Some internet security software will notify you that you’re about to visit a harmful site.
- Don’t open or accept a link in an email unless you trust that it comes from an authorized source.
- Don’t install or download the programs if you don’t have trust in the publisher.
- Don’t click on the pop-up notifications or windows that offer free programs
- Don’t ever click a link in an email unless you know exactly what it is.
advertisement


















Kinza Rao – Associate Software Engineer